Phishing
Phishing is the most common form of cyberattack, and often leads to successive, more severe attacks. Learning to identify and respond to phishing is an essential digital skill and a cornerstone of keeping yourself and others safe.
“Phishing” has evolved into a catch-all term for malicious deception with the goal of compromising sensitive information or systems. Phishing usually happens through email, but can start on social media, over text, by phone, etc. Most often, phishing attacks will ask you to click on a link, but other times the attack happens by convincing you to sign in on a fake login page, send MFA verification codes, fill out a form, download a malicious file, or simply respond with some requested information.
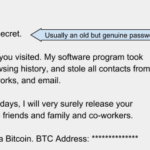
The most frequent attacks are deliberately transparent with clear warning signs—a strategy designed to find very susceptible targets. However, attacks are also frequently tailored to the target—they might impersonate Luther’s Common Login Portal, or mimic alert messages from services like Zoom, or even pretend to be a college employee you know well. Phishing often exploits our deepest human instincts—they pique our curiosity, instill fear, claim urgency, and impersonate people or institutions that we trust.
It’s essential to recognize that phishing doesn’t occur in isolation—it is not petty theft or vandalism whose harm is contained to individuals—instead, it is the engine that powers massive scale attacks on institutions and infrastructure. When phishing is successful, it rapidly turns into successive attacks. Even victims “with nothing worth stealing” are lucrative targets—often the attacker will try to phish the victim’s friends and family and colleagues, who are predisposed to trust the victim and miss signs of danger.
Phishing is usually just the first part of a more complicated attack. Left unchecked, successful attackers will lock out the victim and will use their account to pry open everything else the victim can access, like online accounts, work accounts, financial assets, and everything else needed for full identity theft. The chain of phishing continues until the attacker compromises someone with particularly sensitive or expansive professional access, and then pivots to sophisticated attacks on their workplace. In other words, the hapless, misspelled email we easily recognize as phishing is part of the same apparatus that launches the sort of cyberattacks that make the news and shape world events. We don’t take phishing seriously because it threatens us, we take it seriously because it threatens our community and our world at large.
If you’re a victim of phishing
- Reset your password immediately if you clicked a link or downloaded an attachment, even if you didn’t enter your password anywhere—just visiting an unsafe website is enough. If you merely replied to the message, you don’t need to reset your password. Your new password should bear no resemblance to the old one, and if you used your old password or a variation of the password on other sites, change your password there, too.
- Forward the message to the Technology Help Desk, ideally including the raw “original message” (On the Gmail website, it’s inside an email’s “more” menu).
If you suspect phishing
Report suspected or confirmed phishing emails with PhishNotify, Luther’s one-click reporting tool. Look for the red fish icon in your list of Gmail add-ons:
- On a computer, PhishNotify will usually be in a sidebar on the right;
- On the Gmail app for Android and iOS, look inside the “more” menu while you have an email open.
- Other apps or personal email accounts won’t have PhishNotify, but you should report it anyway by forwarding it to the Technology Help Desk. It’s helpful to say whether you’ve interacted with the message.
Note: The first time you use PhishNotify, you’ll need to grant it permission to interact with your email.
PhishNotify is also a learning tool—it will let you know when you report a fake phishing email sent by ITS, and reports of any kind will lower your need for phishing-focused training in the future, maybe exempting you altogether.
Identifying phishing
Learning to recognize phishing is a cornerstone digital skill. Here are some common things to look for, particularly with email:
Inspecting links
The best way to identify phishing is to inspect links before you click them. Inspect a link by copying or hovering over it. Specifically, pay attention to whether the “domain” portion of the link is trustworthy. The domain is the portion of the URL that includes the suffix (.edu, .com, etc.) and everything up to the preceding period (e.g. https://subdomain. luther.edu /randompage.html).
Sometimes a trustworthy domain can still host something dangerous (like a Google form that asks for your password), but often the disparity will be obvious: A “Zoom” link that doesn’t go to zoom.us or zoom.com, a “UPS tracking” link that goes to ups-tracking.com instead of ups.com. Sometimes it can be hard to know whether a domain is real, and searching things like “safe ups-tracking.com” will return helpful information.
If you do click a link and then realize that it’s unsafe, it’s too late—Malware can infect your device just by visiting a page. See the section above: “If you’re a victim of phishing”
Sender’s display name doesn’t match email address
Attackers will often change the sender’s display name in an effort to make an email seem more legitimate. For example, a compromised account might masquerade as the Security office by simply changing the display name to “Campus Security”.
Generic greeting
Most phishing campaigns rely on volume rather than personalization. Phishing emails often aren’t addressed to you with appropriate familiarity. They might instead be addressed to “Sir or Madam”, “Mr…” or “Ms…”, or simply omit a name entirely (e.g. “Dear,”).
Incorrect grammar, syntax, spelling
Phishing attacks sometimes use incorrect language. This is often deliberate: those who aren’t suspicious of blatant language problems are re-targeted in future attacks.
Sense of urgency
Attackers try to compel you to action before you have had time to become suspicious and use your better judgement. Content will often try to evoke fear, panic, and greed. Topics might be about resetting passwords, submitting paperwork, quickly fleeting windows of opportunity, or a “final notice”.
Unexpected
Generic phishing is always unexpected; spear phishing will try to blend in with your normal life. If you aren’t expecting the communication, you should be suspicious.
Attachments
Never open attachments until you’re sure that an email is safe—Attachments that contain malware can run as soon as they are downloaded. PDFs, Zip files, and Microsoft Office documents are commonly used to disguise malware. If you’ve downloaded or opened an attachment, notify the Technology Help Desk immediately and begin an anti-virus scan. Simply deleting the file is not sufficient—malware distributed like this assumes that the original file will be deleted, so it embeds new malware packages deep into the device as soon as it is opened.
Technology Help Desk
Preus Library
Main Level
700 College Dr
Decorah, IA 52101
Spring Semester
February 4 – May 21
M–Th: 7:30 am – 9:00 pm
F: 7:30 am – 5:30 pm
Sa: 2:00 pm – 5:30 pm
Su: Noon – 9:00 pm
Phone: 563-387-1000